Many of us have been there, we manage our ESXi hosts via vCenter like a responsible adult. But alas, one day, vCenter goes haywire and is inaccessible and requires an admin to hit up their local ESXi hosts. If these ESXi hosts were not joined to Active Directory, only the local root account remains for authentication. There is no other way to connect to these hosts other than via the root account. And if this root password is lost, then there is trouble. In these cases, the following tutorial explained below can be helpful.
Please Note: VMware does not officially support this method. VMware states that the only supported way to reset an ESXi password is by reinstalling the host. This was tested on ESXi 6.5.
In this tutorial we will be using a Live Linux CD/DVD/USB, to change the root password on your ESXi host. ESXi saves the root password encrypted in a password file located in /etc/shadow . We will be removing the password hash in located in 2 partitions in order to create a new password in the DCUI console.
Step 1
Download a Live Linux ISO. I chose Gparted Live for this task.
Step 2
Burn the Gparted Live ISO to a USB or CD/DVD. For this step I used Rufus, a tool which allows you to create bootable USBs from ISO images.
Step 3
Insert the Gparted Live Media to your ESXi host, make sure your server is able to boot off CD/DVD or USB. Power on the server. Continue by following the on screen instructions in order to complete the boot process. Once completed you should reach the desktop and be able to see all of the ESXi partitions.
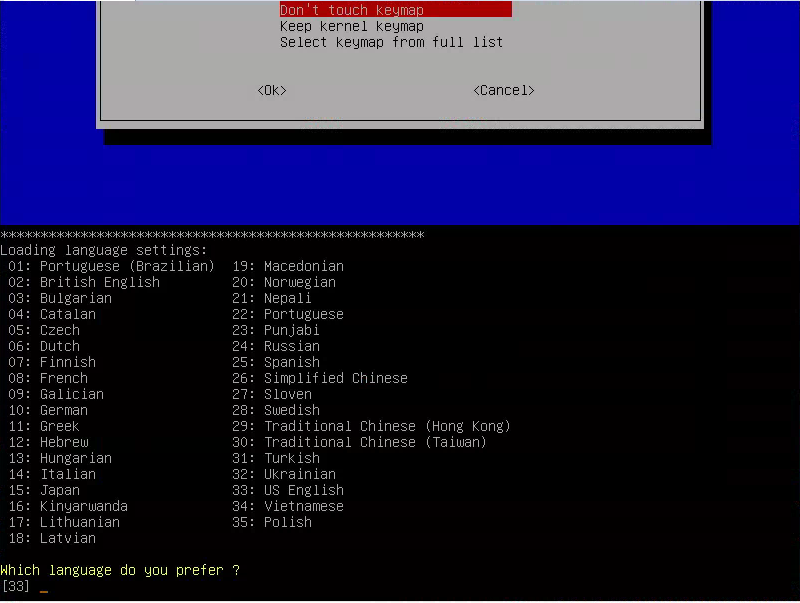
Gparted Boot Screen
Step 4
Locate the 2 partitions sized 249.98MB. The /dev/sda5 and /dev/sda6 are what we’re after assuming you installed ESXi on the first available hard drive/ssd. This could differ if, for example, you installed ESXi on a USB device or SD card. We will be editing the /dev/sda5 partition first followed by the /dev/sda6.
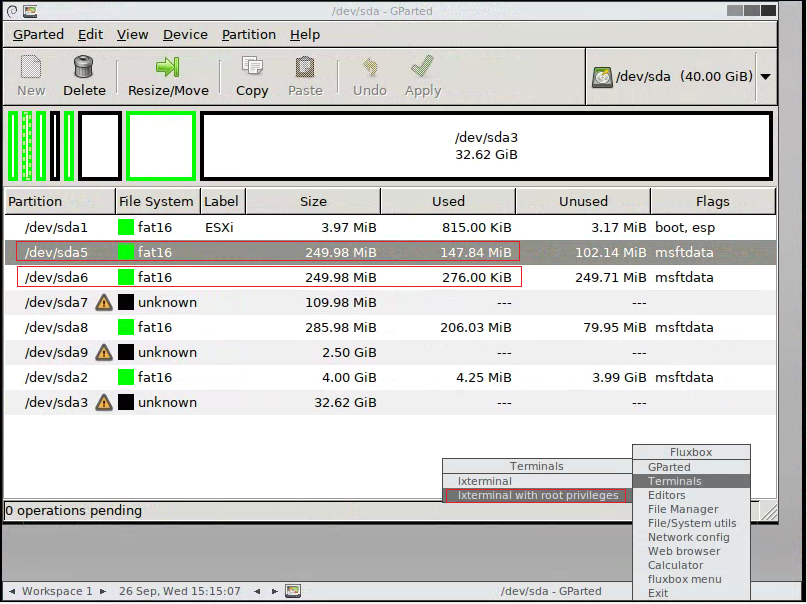
Gparted showing the partitions found on disks
Step 5
Right click on the desktop to open a terminal window with root privileges and run the following commands in the order as listed.
|
1
2
3
4
5
6
7
8
9
10
11
|
sudo su
mkdir /boot /temp
mount /dev/sda5 /boot
cd /boot
cp state.tgz /temp
cd /temp
tar –xf state.tgz
tar –xf local.tgz
rm *.tgz
cd etc
vi shadow
|
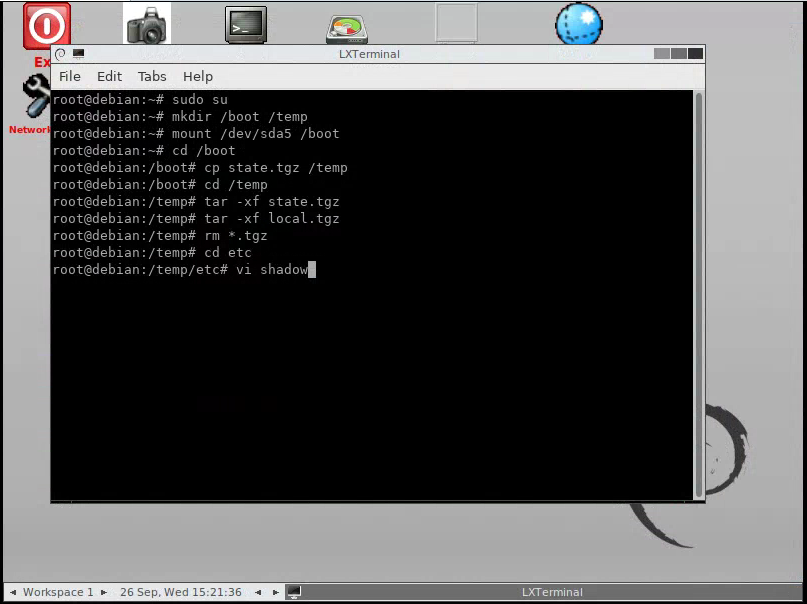
First batch of commands
Step 6
We are using vi command to edit the shadow password file. Move to the line starting with the root and delete the hash string between the first 2 colons. Use the Delete key. When complete type :wq followed by Enter key.
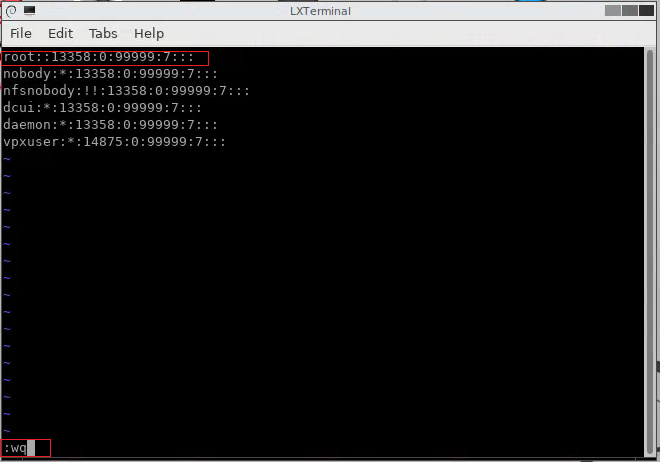
Password file after hash deletion
Step 7
Continue by running the following batch of commands.
|
1
2
3
4
5
6
|
cd ..
tar –cf local.tgz etc/
tar –cf state.tgz local.tgz
mv state.tgz /boot
umount /boot
reboot
|
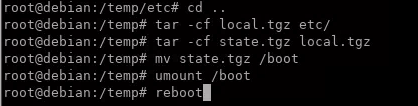
Second batch of commands
Step 8
Boot back into the Gparted Live media. We will be repeating steps 5-7 except we will be editing the /dev/sda6 partition rather than /dev/sda5. The only difference in this process we will be changing command 3 in Step 5 to mount the correct partition.
| 3 |
mount /dev/sda6 /boot
|
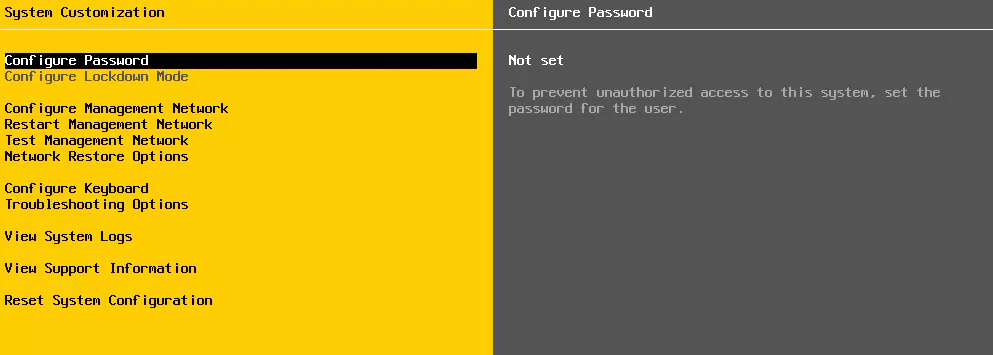
Step 9
Remove the Gparted media and boot the ESXI host. Once the ESXi host has completed booting, log on as root from the DCUI console. You should be able to log in without typing in a password. Now you may configure a new password.
Although this method is not officially supported by VMware, it works on various versions of ESXI. The reasoning is likely because VMware doesn’t want you to modify ESXi installation files. But considering you are doing is just zeroing out a password hash file in this procedure, it is unlikely you will run into any issues.
-Reubin Huckle





This saved me … All other articles say sda5 .. but after reading your article, I had hope and after seeing shadow file on sda6, I was crazy happy. After updating the file, it worked like a charm. Thanks for this post.. Keep writing.
Thank you!
Thank you very much.
I have a comment: I tried and see that we don’t need to do for dev/sda6. It made me confuse when I mounted dev/sda6 and haven’t seen files as on your instruction.